In Part1 of the Wifi IR Blaster Hack article, we learned how to flash the Tasmota firmware to a generic WiFI IR-Blaster, and get to the main Tasmota interface. This article will follow with configuration and usage.
Thing’s you’ll need to proceed:
- WIFI-IR Blaster with Tasmota flashed, powered on, connected to your network
- Access to the Tasmota UI via web browser
- Any IR (infrared) remote control for testing or initial setup. Can be anything, TV remote, receiver remote, etc.
- A quick way to confirm your remote is IR: Open your cellphone camera, point the remote facing the camera and press a button. If you can see a faint flash coming from the remote (from the cellphone camera), it’s an IR remote.
Initial Configuration
Note: The following uses a more recent build of Tasmota (10.1.0) here than the previous module (9.1.0).
Open a web browser, and get to the config page by using the device’s IP address (or hostname, if you’ve set it in the Configure Wifi configuration setting earlier)
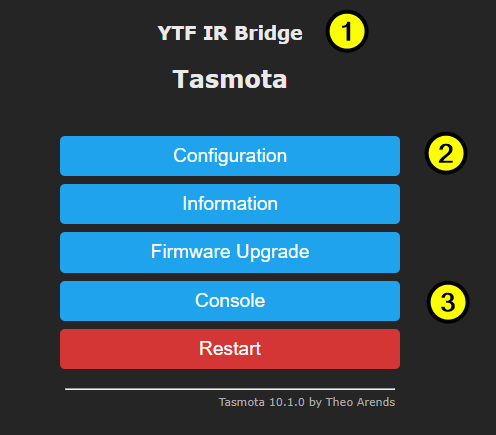
Chances are after first setup, [1] above will appear as “Generic Module”. Let’s set it up to be the proper configuration.
Click Configuration [2], then click Configure Module, from the Module Type dropdown, choose YTF IR Bridge (62). Finally click Save, wait a bit, then it’ll forward you to back to the main screen when done.
Now let’s enter the console where we can start playing around and making sure we can receive IR signals. Click the Console [2] button.
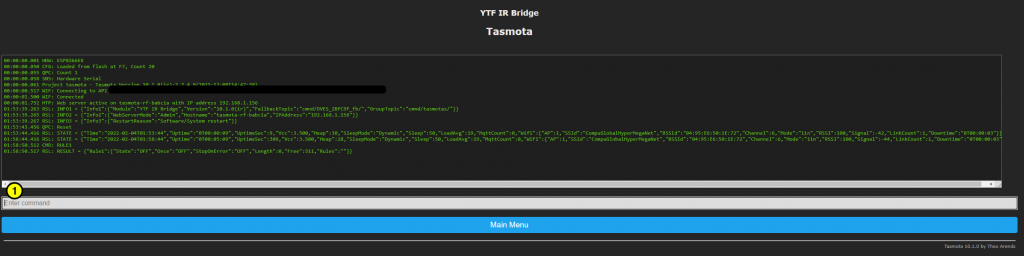
The Tasmota live Console can look intimidating, but it’s a really powerful way to send commands, view status, and program configuration and rules beyond the main interface capabilities.
Capturing an IR remote press code
The tasmota-ir firmware loaded have a bunch of built in IR protocols. First we have to see if your remote keypress is in this IR protocol list, and this can be tricky to find out because of timing (e.g. pressing the button too long, or incorrect interpretation.)
Point your remote at the WIFI-IR blaster, choose a button to test on your remote and press a button. Watch the console as you do this, press the remote button a few times. You’ll see something like one of the two outputs below
02:54:16.630 RSL: RESULT = {"IrReceived":{"Protocol":"EPSON","Bits":32,"Data":"0x4BB640BF","DataLSB":"0xD26D02FD","Repeat":1}}If you get a response with "Protocol":"UNKNOWN", then it won’t be possible with the current setup to capture and re-send the IR data. It’s possible, but takes a bit of work and is beyond the scope of this document. (Basically, need to flash the Portisch firmware to get the rfraw command. I might make an article on that if there’s interest)
Make a web-request URL to blast your IR code
To make a web request link, we first need to encode the command (starting with "Protocol") above into URL-encoded format. Just copy and get the encoded version over at urlencoder.org.
So we pass the following command to urlencoder.org:
{"Protocol":"EPSON","Bits":32,"Data":"0x4BB640BF","DataLSB":"0xD26D02FD","Repeat":1}Copy that encoded output, then paste it RIGHT AFTER this text:
http://<ipaddress>/cm?cmnd=IRSend%20So in the end, you’ll have something like:
http://<ipaddress>/cm?cmnd=IRSend%20%7B%22Protocol%22%3A%22EPSON%22%2C%22Bits%22%3A32%2C%22Data%22%3A%220x4BB640BF%22%2C%22DataLSB%22%3A%220xD26D02FD%22%2C%22Repeat%22%3A1%7DNote: replace the <ipaddress> field above to the IP or hostname of your WIFI-IR blaster obviously.
That’s pretty much it! Use that URL above in any way you like (call it from webapp, script, etc.) and the WIFI-IR blaster will blast that code
Example Usage
One example is to make a completely custom Roku Remote using the RokuRunner webapp and IR command URLs.
Also, you can accomplish some pretty cool stuff without any external apps, etc. with Tasmota Rules, which are simple scripts that you can program into Tasmota.
Conclusion
Tasmota is a very cool, useful, powerful modification for many IOT devices. But if you’re reading this far and you’re new to it, it can be a bit overwhelming.
